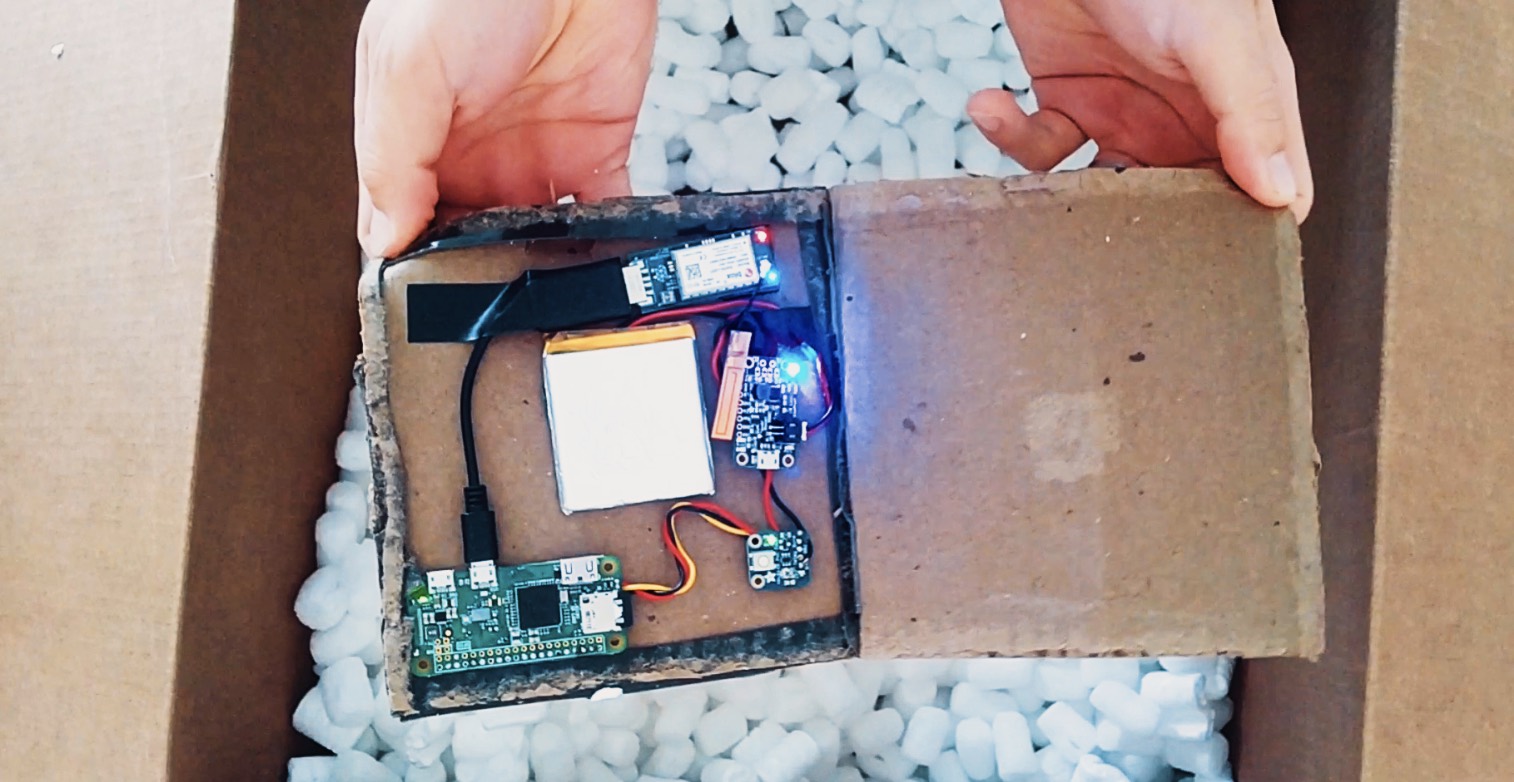
Medan nästan all uppmärksamhet riktas mot traditionella online-metoder för dataintrång, så rapporterar säkerhetsforskarna på IBM X-Force Red om en lucka de upptäckt: Post/budpaket med inbyggd utrustning för att komma åt WiFi-nätverk.
BoingBoing förklarar:
The device scans for visible wifi networks; once it senses a network associated with its target (indicating that it has arrived on the target company’s premises), it alerts its controllers over the cellular radio, and then scans the local wifi for instance in which users’ devices are initiating new connections to the network. It captures the handshake data from these connections, transmits them over the cellular network to its controllers, and they can then crack the password offline, send login credentials to the warshipping device, login to the target network, and attack the network from within.
Länkar:
• With warshipping, hackers ship their exploits directly to their target’s mail room »
• Warshipping: attack a target network by shipping a cellular-enabled wifi cracker to a company’s mail-room »